Adware/Fakeapp!Android
 Analysis
Analysis
Adware/Fakeapp!Android is a piece of adware targetting Android mobile phones.
The malicious package comes disguised as a game like Temple Run however, contains no legitimate activity. Instead, in the background, it forces the user to share the app using her facebook and/or twitter account.
Technical Details
The main application is called "Temple Run" (or could be another game) and comes in the package "com.templefungame.free" or "com.gameguides".
When launched, the user is shown a screen as seen in Fig1
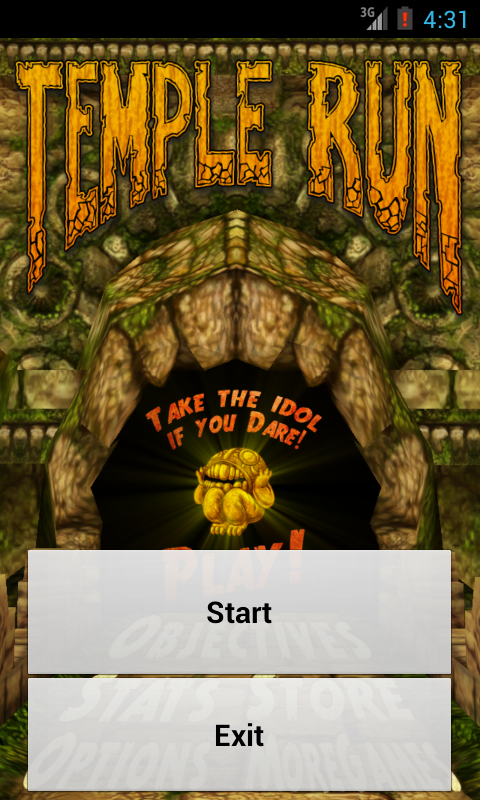
Fig1 : Fake Temple Run launcher
Next, the application checks if the user has the facebook and/or twitter applications forced. If yes, the user is forced to share the application using these applications.
If the user clicks on "Start" in Fig1, a screen as seen in Fig2 is shown.
The application also sends a request to the URL "hxxp://[REMOVED]/settings/templerunfake_settings.json" that downloads a list of settings that include the advertisement that can be seen at the top in the pull down menu (ref Fig2)
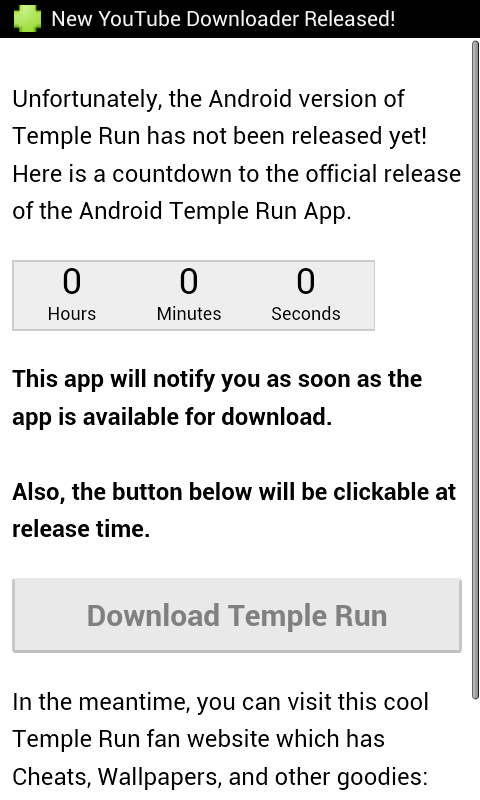
Fig2 : Fake Temple Run installer
In the background, the user is registered with the controversial AirPush advertisement SDK.
The application also registers the phone with the LeadBolt Ad Controller SDK, both of which download several advertisements to the user's phone.
It also places several shortcuts on the Home screen of the phone as seen in Fig3.
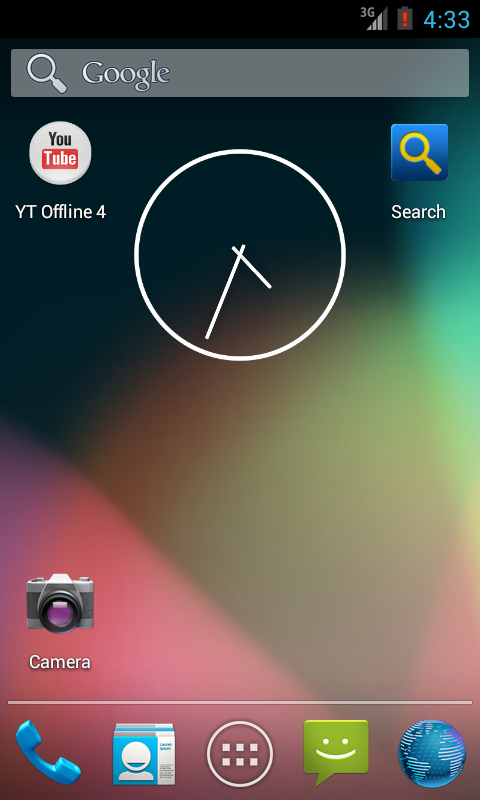
Fig3 : "YT Offine4" and "Search" shortcuts placed on the Home screen
Permissions required by the application:
- INTERNET
- RECEIVE_BOOT_COMPLETED
- ACCESS_NETWORK_STATE
- ACCESS_FINE_LOCATION
- ACCESS_COARSE_LOCATION
- WRITE_EXTERNAL_STORAGE
- READ_PHONE_STATE
- ACCESS_LOCATION_EXTRA_COMMANDS
- VIBRATE
- INSTALL_SHORTCUT
- WAKE_LOCK
- READ_HISTORY_BOOKMARKS
- WRITE_HISTORY_BOOKMARKS
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |