MSIL/Boom.1FD2!tr.ransom
 Analysis
Analysis
MSIL/Boom.1FD2!tr.ransom is a generic detection for a Ransomware Boom trojan.
Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- %Temp%svchost.exe : This file is currently detected as W32/Boom.1FD2!tr.ransom .
- %Temp%\bdx48saerp3j6l1.exe : This file is currently detected as W32/Boom.1FD2!tr.ransom.
- how to decrypt files.txt : This text file will serve as ransom note. It is dropped in every infected folder.
- This Ransomware attempts to stop the explorer.exe process from running.
- Affected files of this Ransomware will use the filenaming format {Originalfilename.Ext}.Boom
- This malware was also observed to affect/encrypt files located on shared drive within the same subnet.
- This malware may apply any of the following registry modification(s):
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Currentversion\Run
- Alcmeter = %Temp%\bdx48saerp3j6l1.exe
- HKEY_LOCAL_MACHINE\Software\Wow6432node\Microsoft\Windows\Currentversion\Run
- Alcmeter = %Temp%\bdx48saerp3j6l1.exe
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Currentversion\Run
- Below is an illustration of the malware's Ransom notes:
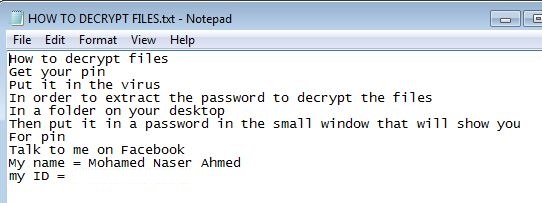
- Figure 1: Ransom note .
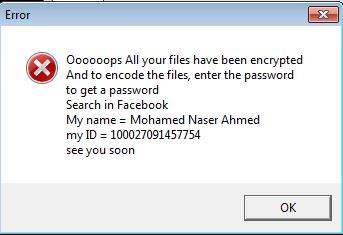
- Figure 2: Message prompt .
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |