Android/Smstibook.A!tr
 Analysis
Analysis
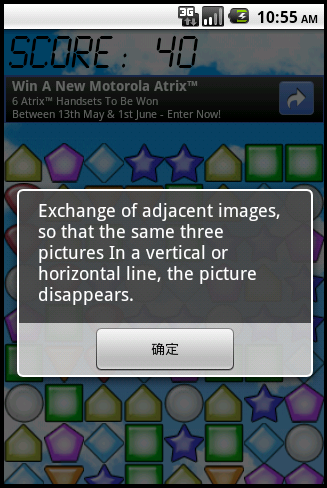
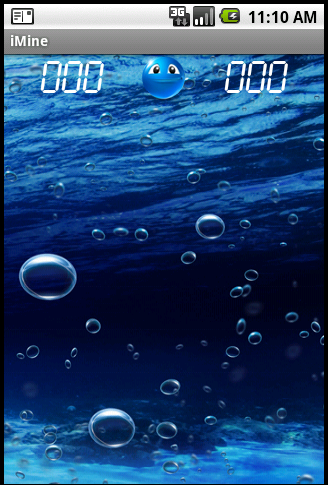
Android/Smstibook.A!tr is a Trojan for Android mobile phones. It trojans several applications or games (calendar, figure matching game, mining - See Figures 1, 2 and 3) but, in background, sends an SMS message to a Chinese Service Provider. The application and games work correctly.
 |
 |
 |
| Figure 1. Main screen for iMatch - trojaned application | Figure 2. Main screen for iMine - trojaned application | Figure 3. Main screen for iCalender - trojaned application |
Technical Details
Depending on the sample, the SMS message is not immediately sent. For instance, the victim might have to click 5 times on an image, or start over a new game to trigger SMS sending.
The SMS message is sent to a Chinese Service Provider. Its number depends on the malicious, but for instance, it is something like 106618xxxx. Its content is 921X2.
After the message is sent, a marker is written to a file in the malware's shared preference directory (/data/data/<APPNAME>/shared_prefs/iBookT.xml). This marker prevents the SMS message from being re-sent other times. See the value "Y" for iBookS below.
<?xml version='1.0' encoding='utf-8' standalone='yes' ?> <map> <string name="iBookS">Y</string> <long name="iBookN" value="1305198696938" /> </map>The value of iBookN corresponds to the current time.
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| Extreme | |
| FortiAPS | |
| FortiAPU | |
| FortiMail | |
| Extreme | |
| FortiSandbox | |
| Extreme | |
| FortiWeb | |
| Extreme | |
| Web Application Firewall | |
| Extreme | |
| FortiIsolator | |
| Extreme | |
| FortiDeceptor | |
| Extreme | |
| FortiEDR |