W32/Kryptik.FWMX!tr.ransom
 Analysis
Analysis
W32/Kryptik.FWMX!tr.ransom is a generic detection for a Locky Ransomware trojan.
Since this is a generic detection, malware that are detected as W32/Kryptik.FWMX!tr.ransom may have varying behaviour.
Below are examples of some of these behaviours:
- This ransomware is usually dropped by VBA/Agent.EDD!tr.dldr.
- This malware will drop lukitus-[Random].htm all over the affected hosts that serves as the ransom notes.
- Based on our tests this Ransomware usually resides as undefinedAppDataundefined\Local\Temp[Random].exe.
- This malware will also drop undefinedUserundefined\Desktop\lukitus.bmp, another ransom note for the affected user.
- The following registry modifications are applied:
- HKEY_CURRENT_USER\Control Panel\Desktop
- Wallpaper = "undefinedUserundefined\Desktop\lukitus.bmp"
- HKEY_CURRENT_USER\Control Panel\Desktop
- Encrypted files are renamed using the filename format XXXXXXXX-XXXX-XXXX-XXXXXXXX-XXXXXXXXXXXX.lukitus, where X is any alphanumeric character.
- Below is an example of the Ransom notes:
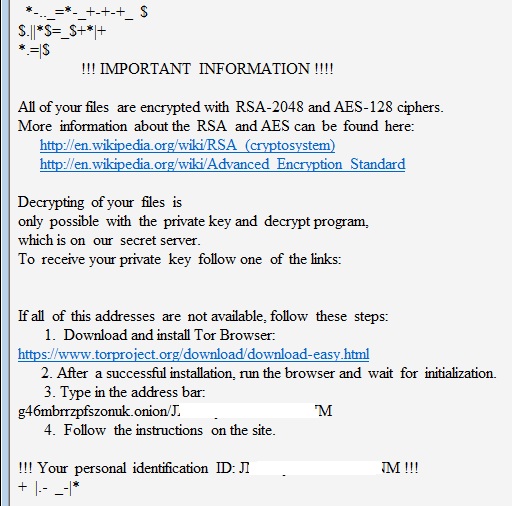
- Figure 1: Ransom notes.
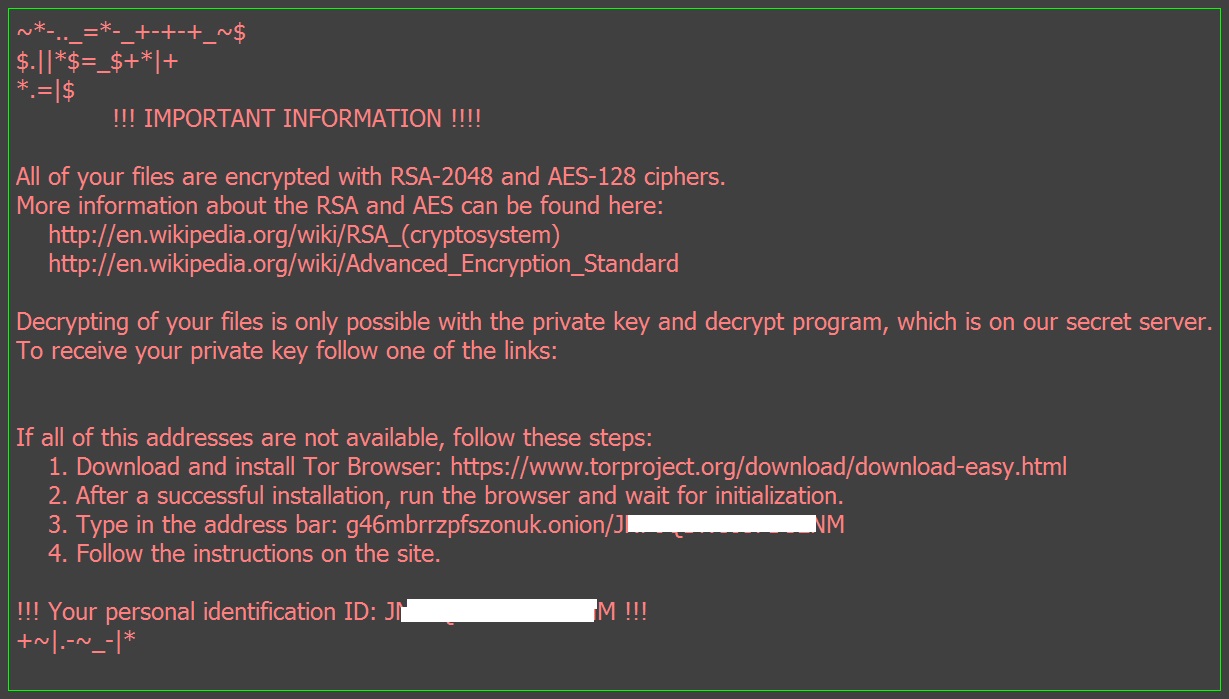
- Figure 2: Ransom notes.
 Recommended Action
Recommended Action
- Make sure that your FortiGate/FortiClient system is using the latest AV database.
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extended | |
| FortiClient | |
| FortiMail | |
| FortiSandbox | |
| FortiWeb | |
| Web Application Firewall | |
| FortiIsolator | |
| FortiDeceptor | |
| FortiEDR |