 Analysis
Analysis
W32/Troldesh.71B6!tr.ransom is a generic detection for a Troldesh Ransomware trojan.
Since this is a generic detection, this malware may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware may drop any of the following file(s):
- README[X].txt : where X is any number, this text file is dropped all over the affected hosts and serves as ransom notes, .
- %ProgramData%\Windows\csrss.exe: This file is a copy of the original malware itself.
- %CurrentPath%\CFGDEMO.CFG : This file is a none malicious INI text file.
- %AllUsersProfile%\Windows\csrss.exe : This file is a copy of the original malware itself.
- %CommonAppData%\windows\csrss.exe : This file is a copy of the original malware itself.
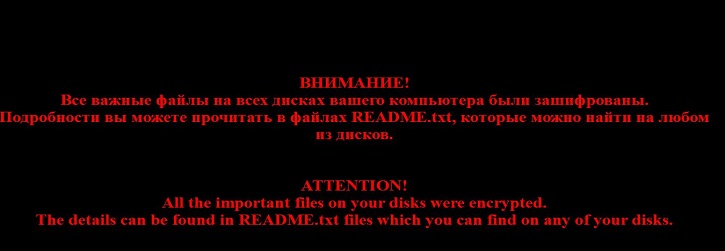
- %AppData%\Roaming\xxxxxxxxxxxxxxxx.bmp : This image file will serve as ransom notes.
- This malware may connect to any of the following remote sites(s):
- 15{Removed}.35.32.5
- 17{Removed}.25.193.9
- 19{Removed}.109.206.212
- 19{Removed}.23.244.244
- 12{Removed}.31.0.39
- 13{Removed}.188.40.189
- 8{Removed}.163.131.198
- 7{Removed}.73.17.194
- Affected files of this Ransomware may use any of the following filenaming format:
- [Hash]=.XXXXXXXXXXXXXXXXXXXX.crypted000007, where X is any alphanumeric character.
- {Orginal name}[Random]=.xtbl
- {Original name}[Random].UID.better_call_saul, Here UID is identifier unique to each infection.
- This malware was also observed to affect/encrypt files located on shared drived within the same subnet.
- This Ransomware also changes desktop background to ransom notes using %AppData%\Roaming\xxxxxxxxxxxxxxxx.bmp
- Affected victimes of this Ransomware are redirected by the attacker via:
- Novikov.Vavila@gmail.com
- decode00001@gmail.com
- decode00002@gmail.com
- Korzhenevskiy.Kirsan@gmail.com
- pilotpilot088@gmail.com
- Our tests indicate that some instances of this malware may have delayed effects of applying its File Encryption payload on the affected hosts.
- This malware may also apply the following autorun registries:
- HKEY_CURRENT_USER\Software\Microsoft\Windows\Currentversion\Run
- Client Server Runtime Subsystem = %ProgramData%\Windows\csrss.exe
- Client server runtime subsystem = %AllUsersProfile%\windows\csrss.exe
- Client server runtime subsystem = %CommonAppData%\windows\csrss.exe
This automatically executes the dropped file every time the infected user logs on.
- Below are some illustrations of the malware's Ransom notes:
 Analysis
Analysis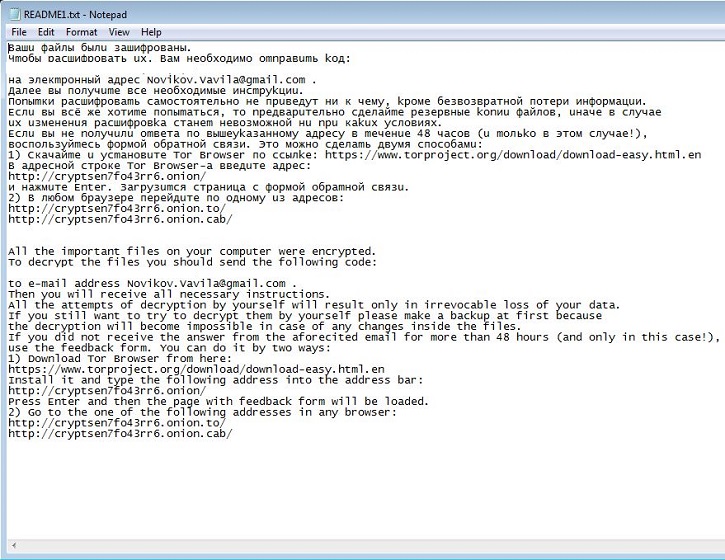
 Recommended Action
Recommended Action Telemetry
Telemetry